Don't be the next company on the news for running EOL infrastructure.
EOL dates and CVE data for operating systems and network hardware. One API call. Sourced from vendor bulletins, not generated by AI.
No sales calls. No agents. No testimonials, we don't have your email address. Run your business.
Supported Platforms
More: All Vendors
Get Started in 5 Minutes
Create an Account
Anonymous signup. No email required.
Set Up TOTP
Scan a QR code with your authenticator app. Save your backup codes.
Choose Capacity
Monthly plans start with Shared: 1 req/s sustained, 1 concurrent request.
You're Live
Query the API or run the open source collector.
Why Network-Audit.io
Deterministic, not probabilistic
Ask ChatGPT when Ubuntu 20.04 LTS hits EOL. You might get the right response, you might get it a year off. Ask our API. You'll get the exact date with a source URL attached.
Every distro reports differently. We don't care.
Debian publishes release dates on a wiki. RHEL buries them in a knowledge base. We normalize all of it into one consistent API response.
Your data never leaves your network
Our API receives a version string. That's it. No configs uploaded. No inventory files. There's nothing to breach because we never had it.
Built for engineers, not executives
REST API with OpenAPI docs. No demos. No sales calls. Get an API key and try our open source collector.
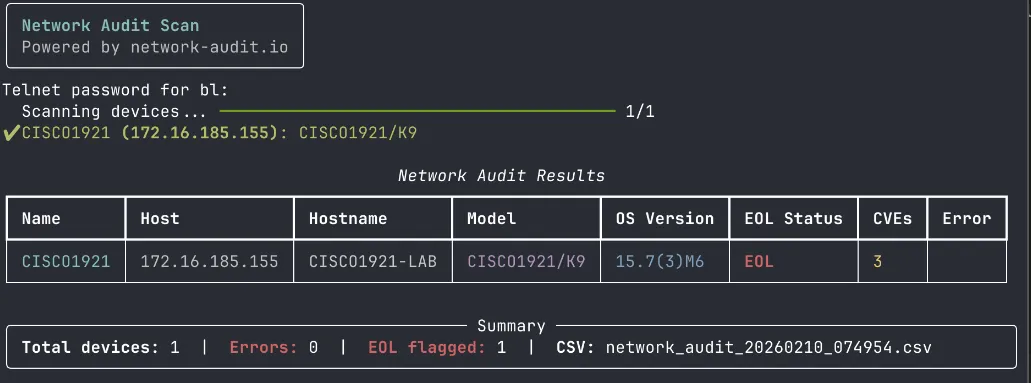
Example Output
Real collector output. Click to expand.
Cisco 2911
{
"name": "core-router",
"host": "192.168.1.1",
"hostname": "CORE-RTR-01",
"model": "CISCO2911/K9",
"os_version": "15.7(3)M8",
"eol_status": "EOL",
"eol_details": {
"end_of_sale": "2017-12-09",
"eol_announce": "2016-09-09",
"last_ship": "2018-03-09",
"last_support": "2022-12-31",
"last_sw_support": null,
"security_support": "2020-12-08",
"sw_maintenance": "2020-12-09"
},
"cve_count": 14,
"eol_raw": {
"status": "success",
"data": {
"vendor": "cisco",
"model": "CISCO2911/K9",
"milestones": {
"end_of_sale": "2017-12-09",
"eol_announce": "2016-09-09",
"last_ship": "2018-03-09",
"last_support": "2022-12-31",
"last_sw_support": null,
"security_support": "2020-12-08",
"sw_maintenance": "2020-12-09"
},
"status": "eol",
"is_eol": true,
"days_until_eol": -1187,
"replacement_model": null,
"source_url": "https://www.cisco.com/c/en/us/products/collateral/routers/2900-series-integrated-services-routers-isr/eos-eol-notice-c51-737831.html"
},
"meta": {
"query_time_ms": 0,
"api_version": "v1",
"database_updated": null
}
},
"cve_raw": {
"data": {
"cves": [
{
"affected_products": "IOS",
"cve_id": "CVE-2025-20363",
"cvss_score": 9,
"cvss_vector": "CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:C/C:H/I:H/A:H",
"description": "A vulnerability in the web services of Cisco Secure Firewall Adaptive Security Appliance (ASA) Software, Cisco Secure Fi...",
"product": "IOS",
"published_date": "2025-09-25",
"severity": "critical",
"severity_rank": 4,
"source_url": null,
"updated_date": null,
"vendor": "Cisco"
},
{
"affected_products": "IOS",
"cve_id": "CVE-2025-20239",
"cvss_score": 8.6,
"cvss_vector": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:N/I:N/A:H",
"description": "A vulnerability in the Internet Key Exchange Version 2 (IKEv2) feature of Cisco IOS Software, IOS XE Software, Secure Fi...",
"product": "IOS",
"published_date": "2025-08-14",
"severity": "high",
"severity_rank": 3,
"source_url": null,
"updated_date": null,
"vendor": "Cisco"
},
{
"_note": "... and 12 more CVEs"
}
],
"model": "CISCO2911/K9",
"total": 14,
"vendor": "cisco"
},
"meta": {
"api_version": "v1",
"database_updated": null,
"query_time_ms": 0
},
"status": "success"
},
"error": null
}Cisco ASA 5505
{
"name": "fw-branch",
"host": "192.168.10.1",
"hostname": "FW-BRANCH-01",
"model": "ASA5505-K8",
"os_version": "9.2(4)",
"eol_status": "EOL",
"eol_details": {
"end_of_sale": "2017-08-25",
"eol_announce": "2017-02-24",
"last_ship": "2017-11-23",
"last_support": "2022-08-31",
"last_sw_support": null,
"security_support": null,
"sw_maintenance": null
},
"cve_count": 7,
"eol_raw": {
"status": "success",
"data": {
"vendor": "cisco",
"model": "ASA5505-K8",
"milestones": {
"end_of_sale": "2017-08-25",
"eol_announce": "2017-02-24",
"last_ship": "2017-11-23",
"last_support": "2022-08-31",
"last_sw_support": null,
"security_support": null,
"sw_maintenance": null
},
"status": "eol",
"is_eol": true,
"days_until_eol": -1309,
"replacement_model": null,
"source_url": "https://www.cisco.com/c/en/us/products/collateral/security/asa-5505-adaptive-security-appliance/eos-eol-notice-c51-738642.html"
},
"meta": {
"query_time_ms": 0,
"api_version": "v1",
"database_updated": null
}
},
"cve_raw": {
"data": {
"cves": [
{
"affected_products": "Cisco NX-OS Software",
"cve_id": "CVE-2025-20191",
"cvss_score": 7.4,
"cvss_vector": "CVSS:3.1/AV:A/AC:L/PR:N/UI:N/S:C/C:N/I:N/A:H",
"description": "A vulnerability in the Switch Integrated Security Features (SISF) of Cisco IOS Software, Cisco IOS XE Software, Cisco NX...",
"product": "Cisco NX-OS Software",
"published_date": "2025-05-07",
"severity": "high",
"severity_rank": 3,
"source_url": null,
"updated_date": null,
"vendor": "Cisco"
},
{
"affected_products": "Cisco NX-OS Software",
"cve_id": "CVE-2025-20241",
"cvss_score": 7.4,
"cvss_vector": "CVSS:3.1/AV:A/AC:L/PR:N/UI:N/S:C/C:N/I:N/A:H",
"description": "A vulnerability in the Intermediate System-to-Intermediate System (IS-IS) feature of Cisco NX-OS Software for Cisco Nexu...",
"product": "Cisco NX-OS Software",
"published_date": "2025-08-27",
"severity": "high",
"severity_rank": 3,
"source_url": null,
"updated_date": null,
"vendor": "Cisco"
},
{
"_note": "... and 5 more CVEs"
}
],
"model": "ASA5505-K8",
"total": 7,
"vendor": "cisco"
},
"meta": {
"api_version": "v1",
"database_updated": null,
"query_time_ms": 0
},
"status": "success"
},
"error": null
}FortiGate 60F
{
"name": "fw-hq",
"host": "10.1.1.1",
"hostname": "FW-HQ-01",
"model": "FortiGate-60F",
"os_version": "7.2.8",
"eol_status": "Not Found",
"eol_details": null,
"cve_count": 36,
"eol_raw": null,
"cve_raw": {
"data": {
"cves": [
{
"affected_products": "FortiOS",
"cve_id": "CVE-2026-24858",
"cvss_score": 9.4,
"cvss_vector": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:H/RL:O/RC:C",
"description": "An Authentication Bypass Using an Alternate Path or Channel vulnerability [CWE-288] vulnerability in Fortinet FortiAnaly...",
"product": "FortiOS",
"published_date": "2026-01-27",
"severity": "critical",
"severity_rank": 4,
"source_url": null,
"updated_date": null,
"vendor": "Fortinet"
},
{
"affected_products": "FortiOS",
"cve_id": "CVE-2025-59718",
"cvss_score": 9.1,
"cvss_vector": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:F/RL:O/RC:C",
"description": "A improper verification of cryptographic signature vulnerability in Fortinet FortiOS 7.6.0 through 7.6.3, FortiOS 7.4.0 ...",
"product": "FortiOS",
"published_date": "2025-12-09",
"severity": "critical",
"severity_rank": 4,
"source_url": null,
"updated_date": null,
"vendor": "Fortinet"
},
{
"_note": "... and 34 more CVEs"
}
],
"model": "FORTIOS",
"total": 36,
"vendor": "fortinet"
},
"meta": {
"api_version": "v1",
"database_updated": null,
"query_time_ms": 0
},
"status": "success"
},
"error": null
}Juniper MX960
{
"name": "core-pe",
"host": "172.16.0.1",
"hostname": "MX-CORE-01",
"model": "MX960",
"os_version": "21.4R3-S5",
"eol_status": "EOL Warning",
"eol_details": {
"end_of_sale": "2021-06-30",
"eol_announce": "2020-06-30",
"last_ship": null,
"last_support": "2026-06-30",
"last_sw_support": null,
"security_support": null,
"sw_maintenance": null
},
"cve_count": 149,
"eol_raw": {
"status": "success",
"data": {
"vendor": "juniper",
"model": "MX960",
"milestones": {
"end_of_sale": "2021-06-30",
"eol_announce": "2020-06-30",
"last_ship": null,
"last_support": "2026-06-30",
"last_sw_support": null,
"security_support": null,
"sw_maintenance": null
},
"status": "warning",
"is_eol": false,
"days_until_eol": 90,
"replacement_model": null,
"source_url": "https://support.juniper.net/support/eol/product/m_series/"
},
"meta": {
"query_time_ms": 0,
"api_version": "v1",
"database_updated": null
}
},
"cve_raw": {
"data": {
"cves": [
{
"affected_products": "Junos OS Evolved",
"cve_id": "CVE-2026-21902",
"cvss_score": 9.8,
"cvss_vector": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H",
"description": "An Incorrect Permission Assignment for Critical Resource vulnerability in the On-Box Anomaly detection framework of Juni...",
"product": "Junos OS Evolved",
"published_date": "2026-02-25",
"severity": "critical",
"severity_rank": 4,
"source_url": null,
"updated_date": null,
"vendor": "Juniper Networks"
},
{
"affected_products": "Junos Space",
"cve_id": "CVE-2025-59978",
"cvss_score": 9,
"cvss_vector": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:H/I:H/A:H",
"description": "An Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting') vulnerability in Juniper Network...",
"product": "Junos Space",
"published_date": "2025-10-09",
"severity": "critical",
"severity_rank": 4,
"source_url": null,
"updated_date": null,
"vendor": "Juniper Networks"
},
{
"_note": "... and 147 more CVEs"
}
],
"model": "JUNOS",
"total": 149,
"vendor": "juniper networks"
},
"meta": {
"api_version": "v1",
"database_updated": null,
"query_time_ms": 1
},
"status": "success"
},
"error": null
}Debian 12
{
"name": "web-server",
"host": "10.0.1.50",
"distro": "debian",
"version": "12",
"pretty_name": "Debian GNU/Linux 12 (bookworm)",
"codename": "",
"lts": false,
"eol_status": null,
"eol_date": null,
"days_until_eol": null,
"is_eol": null,
"api_response": null,
"error": null
}Windows 10
{
"name": "desktop-pc",
"host": "10.0.2.100",
"product": "Windows 10",
"version": "22H2",
"edition": "Pro",
"build": "19045",
"pretty_name": "Microsoft Windows 10 Pro",
"product_slug": "windows",
"version_slug": "10-22h2",
"last_patch_kb": "",
"last_patch_title": "",
"last_patch_date": "",
"eol_status": "eol",
"eol_date": "2025-10-14",
"days_until_eol": 923,
"is_eol": true,
"api_response": {
"status": "success",
"data": {
"product": "windows",
"version": "10 22H2",
"slug": "10-22h2",
"release_date": "2022-10-18",
"eoas_date": "2025-10-14",
"eol_date": "2025-10-14",
"eoes_date": "2028-10-10",
"lts": false,
"build_number": "10.0.19045",
"status": "eol",
"is_eol": true,
"days_until_eol": 923,
"source_url": "https://endoflife.date/windows"
},
"meta": {
"query_time_ms": 0,
"api_version": "v1",
"database_updated": null
}
},
"error": null
}I spent 15 years as a network engineer maintaining EOL and version spreadsheets by hand. I built this to automate that insanity. No bloated tools, no agents, no sales calls. Just an API you can script and know will work every time you run it.
Pricing
Monthly capacity plans for MSP scan workflows. Fixed capacity, predictable spend, and no surprise overages.
| Tier | Rate | Concurrency | Cost | Term | Discount |
|---|---|---|---|---|---|
| Shared | 1 req/s | 1 | $1,000 | Monthly | None |
| Shared | 1 req/s | 1 | $10,000 | Annual | 2 months free |
| Shared+ | 5 req/s | 10 | $2,500 | Monthly | None |
| Shared+ | 5 req/s | 10 | $25,000 | Annual | 2 months free |
| Dedicated | 100 req/s | 1,000 | From $10,000 | Monthly | Contact Us |
Open-Source Collector
Scan your network devices and check them against our API. SSH and Telnet support. Rich CLI output. CSV export. Available on GitHub.
Linux / macOS
curl -fsSL https://network-audit.io/install.sh | sh
Windows (PowerShell)
irm https://network-audit.io/install.ps1 | iex